Books’ “Boiling Cauldron: Cybersecurity Trends, Threats, And Predictions For 2023” in Forbes reads more like a Cauldron of Propaganda
The Forbes piece Boiling Cauldron: Cybersecurity Trends, Threats, And Predictions For 2023 by Chuck Brooks is an interesting read, but reads more like subliminal propaganda or as CNN might say, an example of a cynical strategy. Since he removed a LinkedIn post with a link to the article, after I opined, supports my argument.
Let’s start with the preamble. He writes: “Cyber-attackers will always look for the weakest point of entry and mitigating third-party risk is critical for cybersecurity” Even for non-security professionals, the statement is rhetorical. Thomas Reid in 1786 on “Essays on the Intellectual Powers of Man” wrote: “In every chain of reasoning, the evidence of the last conclusion can be no greater than that of the weakest link of the chain, whatever may be the strength of the rest.” If that’s pretentious, perhaps we can resort to the “lowest hanging fruit” cliché, where that fruit represents the obvious or easy things that can be most readily done or dealt with in achieving success or making progress toward an objective. Security has been and will continue to be a cat-and-mouse game. The implications are that we should not build a $1000 fence for a $1.00 horse. It’s not about the fastest, most expensive, most complex algorithm. Often brute force suffices
Brooks writes: “Consistently, phishing, insider threats, business email compromise, lack of skilled cybersecurity workers, andmisconfigurations of code have been common trends throughout the past decade” Brooks is spot on
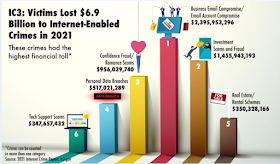
The Federal Bureau of Investigation’s (FBI) 2021 Internet Crime Complaint Center (IC3) Internet Crime Report shows a loss of $6.9 billion in Internet-enabled crimes, the highest in the last five years. The top three cybercrimes reported by victims in 2021 were phishing scams, non-payment/non-delivery scams, and personal data breach.
To Brooks’ credit, this is one of the few times the Inside Threat has been mentioned in the last decade. In remarks prepared on April 27, 2022, for delivery to the Domestic Security Alliance Council, FBI Director Christopher Wray made it clear the counterintelligence threat posed by China is top of mind for the Bureau and did talk about the Inside Threat. But the Inside Threat was conspicuously absent in the FBI 2021 Internet Crime, even though the FBI has a czar in Rachel Rojas, who heads up the Bureau’s Insider Threat Office. In business, we say that whoever controls the chart of accounts, controls the narrative. The FBI controls the cybercrime narrative. Director Wray’s remarks included extoling the virtue of partnerships such as the one with Domestic Security Alliance Council, which the Partnership for Civil Justice Fund, a non-profit, said that espionage facilitated by DSAC treated “protests against the corporate and banking structure of America as potential criminal and terrorist activity,” and said that DSAC was “functioning as a de facto intelligence arm of Wall Street and corporate America.” Jill Sanborn, the former executive assistant director of the FBI’s National Security Branch, has been accused of ordering agents to classify cases as domestic terrorist, when they are not.
In the private sector, Joseph Sullivan, the former Chief Security Officer of Uber Technologies, Inc. (“Uber”), was convicted on Wednesday, October 5, 2022, on charges of covering up a data breach. According to court records, While Sullivan was hired as Uber’s Chief Security Officer (“CSO”) in April 2015 he was involved in two hacks: one in 2014 and another in 2016. When Sullivan was hired, Uber disclosed to the FTC that it had been the victim of a data breach in 2014 and that the breach was related to the unauthorized access of approximately 50,000 consumers’ personal information, including their names and driver’s license numbers. It is possible that Sullivan may have been set up by the previous Uber board of directors, but clearly he was guilty of Insider malfeasance
Brooks correctly states that “..misconfigurations of code have been common trends throughout the past decade. There are two types of organizations: The ones which realize they have been breached & those that don’t. Clearly, insiders with Motive can use lack of proper cyber hygiene as the reason for a breach as in plausible deniability, similar to what Sullivan attempted to do: order his subordinates to be quiet.
Now consider that electionintegrity is a function of the entire voting process, from mail in, voter ID, Voter Registration Lists, hardware, software & so on. The Biggest Threat? The Inside Threat. Threat Actors include corrupt politicians snd employees, hacktivists, money, jealousy, power.
Brooks writes: “In government, securing critical infrastructure and the supply chain has been an evolving priority.” This is not-negotiable. It like saying protecting the air we breathe is an evolving priority and sounds like Congressional Ethics Committee or Government Intelligence – an Oxymoron. It is an example of the $1.00 horse – there’s a reason for identifying critical infrastructure. Critical infrastructure is a term used by governments to describe assets that are essential for the functioning of a society and economy
Brooks continues “The new reality is that most critical infrastructures operate in a digital environment that is internet accessible.” Newsflash: it’s not a new reality. The internet is ancient in terms of technology. Hear of Stuxnet? Stuxnet is a malicious computer worm first uncovered in 2010 and thought to have been in development since at least 2005. Stuxnet targets supervisory control and data acquisition (SCADA) systems and is believed to be responsible for causing substantial damage to the nuclear program of Iran. The worm is widely understood to be a cyberweapon built jointly by the United States and Israel in a collaborative effort known as Operation Olympic Games.
#business #cybersecurity #digital #security #software #supplychain #money #environment #power #economy #infrastructure #email #phishing #DNS #DDS #STUXNET
Agree/Disagree with the author(s)? Let them know in the comments below and be heard by 10’s of thousands of CDN readers each day!